TL;DR: The CA/Browser Forum has adopted a phased schedule that will reduce the maximum validity of public TLS server certificates to 200 days on March 15, 2026, 100 days on March 15, 2027, and 47 days on March 15, 2029. Organizations that automate certificate lifecycle management now will be better positioned for reliability, crypto‑agility, and governance as these deadlines arrive. This post explains why and shares a new 47-day SSL/TLS certificate resources hub to help you prepare.
By 2029, the maximum validity of public TLS server certificates will drop to 47 days, with interim cuts scheduled for 2026 and 2027 by the CA/Browser Forum. That timetable sets the context. The practical question is how to move from an annual renewal cadence to one that happens every few weeks without adding chaos or cost. The answer is not a bigger calendar. It is a well-planned shift to automated certificate lifecycle management, supported by clearer ownership and routine verification. Make those changes and the new cadence becomes a source of resilience rather than a source of outages
Shorter TLS certificate lifespans reward teams that build habits that scale, underscoring the importance of starting off strong with solid planning practices as outlined by Gartner in a 2025 buyers’ guide. Gartner recommends you start by outlining objectives and bringing your certificate inventory into one view. Tie every certificate to an accountable owner. Keep validation predictable. Put issuance and renewal on automation, and pair deployments with checks that confirm the right certificate lands in the right place. Taken together, those habits shorten the lifespan of mistakes and make everyday operations steadier. They are also what the CA/Browser Forum’s phased reductions were designed to encourage.
Why a 47-Day Certificate Resources Hub, and Why Now
While the Gartner guide provides solid advice to set up for success, it can’t possibly provide the scope of resources needed to guide your journey from manual to automated CLM. The volume of inquiries we receive on the topic confirms IT and security leaders are seeking practical, actionable advice, templates, guides, and stories of companies that have made the journey to efficient CLM automation.
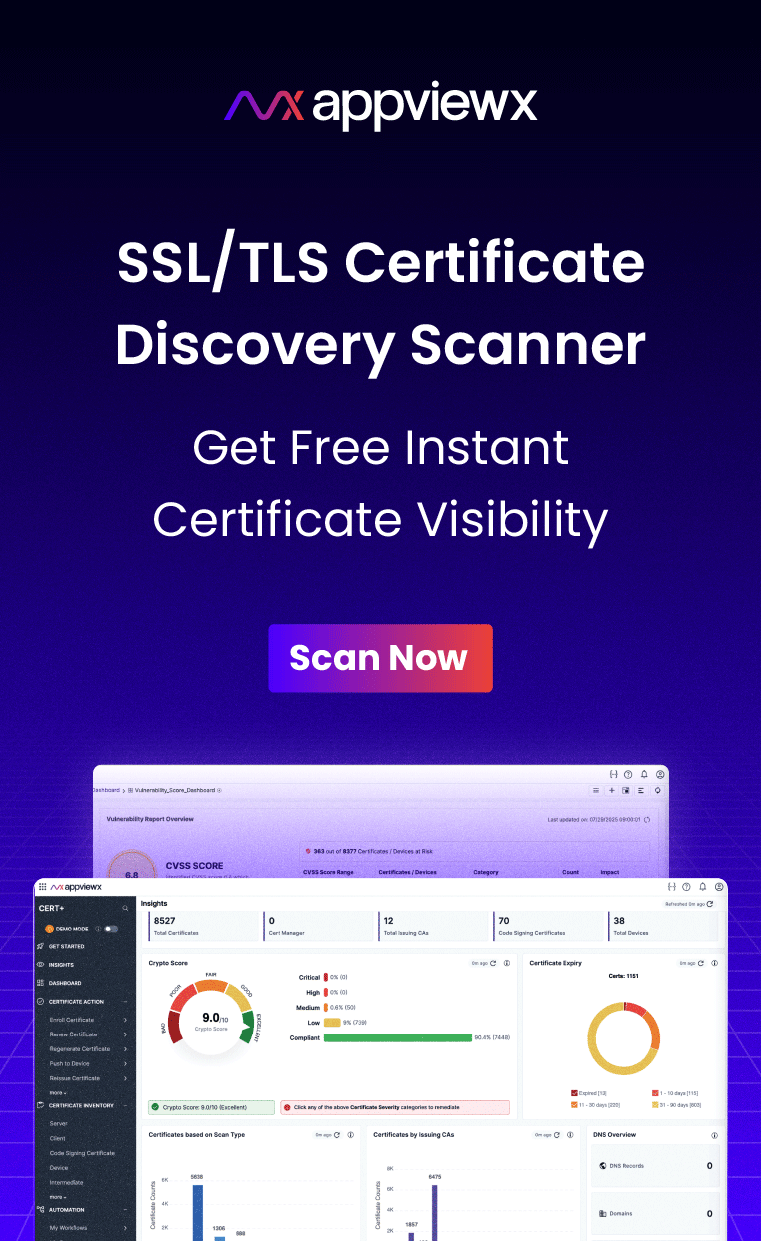
That’s why we’ve compiled these resources in the 47‑Day TLS Certificate Resource Hub, where you will find a calendar of CA/Browser Forum milestones, templates for planning your initiative, quick maturity checklists, case studies from early adopters, and governance mappings you can reuse across environments. We will continue to add templates, checklists, and field notes as standards evolve and the community shares what works. The aim is simple: help you pilot changes, measure progress, and expand automation without risk.
7 Advantages You Gain by Starting Now
You might be tempted to bookmark the 47-day Resources Hub and revisit it as the CA/Browser Forum deadlines start to roll out. But most agree there’s no time like the present to start planning your move. Here are seven reasons and resources to start your journey to 47-day certificate readiness now:
- A stronger security posture with smaller windows of exposure: A certificate captures reality at the moment it is issued and ownership, DNS, and key control can drift. Per CA/Browser Forum guidelines, shorter validity will limit how long outdated information can still be trusted, which lowers risk for site operators and relying parties. The time to start reducing your window of exposure is now.
- Always-current cryptography and faster standards adoption: Frequent renewals make key rotation routine and give you a practical path to switch algorithms as standards evolve. With NIST’s post‑quantum standards now finalized for key establishment and signatures, shorter cycles support faster adoption and clean rollback if guidance changes.
- Fewer misissuance or misconfigured certificates: Validation mistakes and misissuance are rare but real. Re‑checking data more often and limiting certificate lifetimes reduces the time an error can affect users and reduces the blast radius when issues appear.
- Better productivity and fewer errors: According to PacificSource, a U.S.-based healthcare provider, automating certificate management provides significant, measurable productivity and risk reduction by turning certificate tracking and renewals into routine maintenance, rather than a scramble.
- Fewer expiry‑related outages and greater resilience: Expiry is a predictable failure mode. Automation reduces the chance of human‑timing errors and narrows incident scope when they happen. With automation in place, organizations can eliminate the risk of outages due to SSL certificate expiration. That means fewer disruptions and more consistent uptime.
- Governance that proves itself: Short lifespans align with regulatory momentum introduced by DORA and NIST. Mapping certificate processes to CSF outcomes improves auditability and provides a vocabulary to communicate progress to leadership. Early movers can demonstrate readiness and avoid the scramble as deadlines tighten. Short cycles work best when roles, policies, and evidence are clear. Mapping your processes to NIST’s Cybersecurity Framework 2.0 gives you a common language for leadership updates and a structure for audits.
- A futureproof foundation: By adapting now, you will create a foundation for emerging requirements, including post‑quantum transitions and tighter validation timelines. Investing now moves you up the PKI Consortium’s PKI Maturity Model and prepares you for tighter validation windows and new algorithms in the years ahead.
The Bottom Line: 47-Day Mandates Offer An Advantage
The 47‑day mandate is not another IT hurdle to clear. It is an opportunity to run certificate management the way it should work: visible, reliable, efficient and resilient to change. Plan early, automate the routine, and make ownership and policy clear. Do that and you get smaller risk windows, faster cryptographic upgrades, fewer outages, stronger governance, and a clearer future.
Try out the 47-day resources hub today and let us know what you think.