When implementing a certificate lifecycle management (CLM) solution in an organization, the choice between agent-based and agentless architectures is an important decision that can significantly impact the deployment, operations, and scalability of the solution. If you’re unsure which approach aligns with your organization’s needs, this guide breaks down the key differences and advantages of agent and agentless architectures, offering clear insights to help you make an informed decision.
Agentless Architecture
An agentless architecture eliminates the need for software agents to be deployed on individual endpoint devices. Instead, it leverages existing protocols (SSH, WinRM, HTTPS), APIs, or integrations with tools like privileged access management (PAM) to deliver and manage certificates directly on endpoints. This approach helps manage certificate lifecycle processes without requiring additional software installation or maintenance.
Benefits:
- Using Authorized Service Accounts – Leverages vendor native API Tokens, service account, credentials, SSH keys/certificates to access the target device.
- Programmatic Interface as Prebuilt Integrations – Offers ready-to-use integrations for simplified implementation and automation within existing workflows.
- Simplified Deployment – Eliminates the need to install and configure agents on endpoint devices, significantly reducing setup complexity and administrative overhead.
- Reduced Maintenance – Avoids the need for periodic agent upgrades, which can be time-consuming and resource-intensive in large-scale deployments.
- Rapid Implementation – This is particularly beneficial for environments requiring immediate certificate deployment or those where installing agents is prohibited due to policy restrictions. The architecture also allows writing programmable connectors to support any new vendors or versions, enhancing flexibility for CLM use cases.
- Cost Efficiency – Lowers operational costs by removing the need for agent development, deployment, and periodic updates. Rapid deployment allows organizations to realize faster time-to-value and ROI of automated certificate lifecycle management.
- Enhanced Automation – Simplifies and accelerates certificate lifecycle management by automating all processes through a centralized CLM solution, ensuring efficient certificate control and oversight.
- Broad Environment Support – Utilizes device-native tools such as SSH and APIs, ensuring compatibility across a wide range of platforms.
- No Endpoint Dependency: Removes reliance on endpoint-specific software, ensuring uninterrupted operations across diverse infrastructures.
- Minimal Endpoint Resource Usage – As all certificate tasks are performed on the centralized server, agents do not consume local resources on the endpoints, ensuring optimal performance.
- Built-in PAM Integration: Natively integrates with PAM solutions such as CyberArk, Thycotic, and others ensuring compliance with password management policies and streamlined access to target devices.
- Audit and Compliance: Leverages PAM integration to generate detailed session logs and enforce secure access controls for compliance requirements.
Agent-Based Architecture
This approach involves installing lightweight software agents directly on endpoint devices or servers that require certificates. These agents serve as intermediaries, constantly communicating with the certificate management system to fetch, deploy, and manage certificates locally on the device.
Benefits:
- Granular Control – Agents’ direct interaction with endpoints allows control over certificate deployment, renewal, and revocation at the device level, helping fix certificate issues proactively.
- Automation – By automating certificate lifecycle processes directly on devices, agents reduce manual intervention.
- Resilience in Connectivity Challenges – Agents operate asynchronously, allowing certificate updates even with intermittent network issues.
- Environment Support – The architecture excels in complex, large-scale deployments where endpoints have varying configurations, operating systems, or geographical locations.
- Advanced Security Measures – Agents can provide additional security features such as encrypted local storage for private keys and secure access to certificates.
- Cross-Network Capabilities – Agents are effective in environments with segmented networks or restricted connectivity
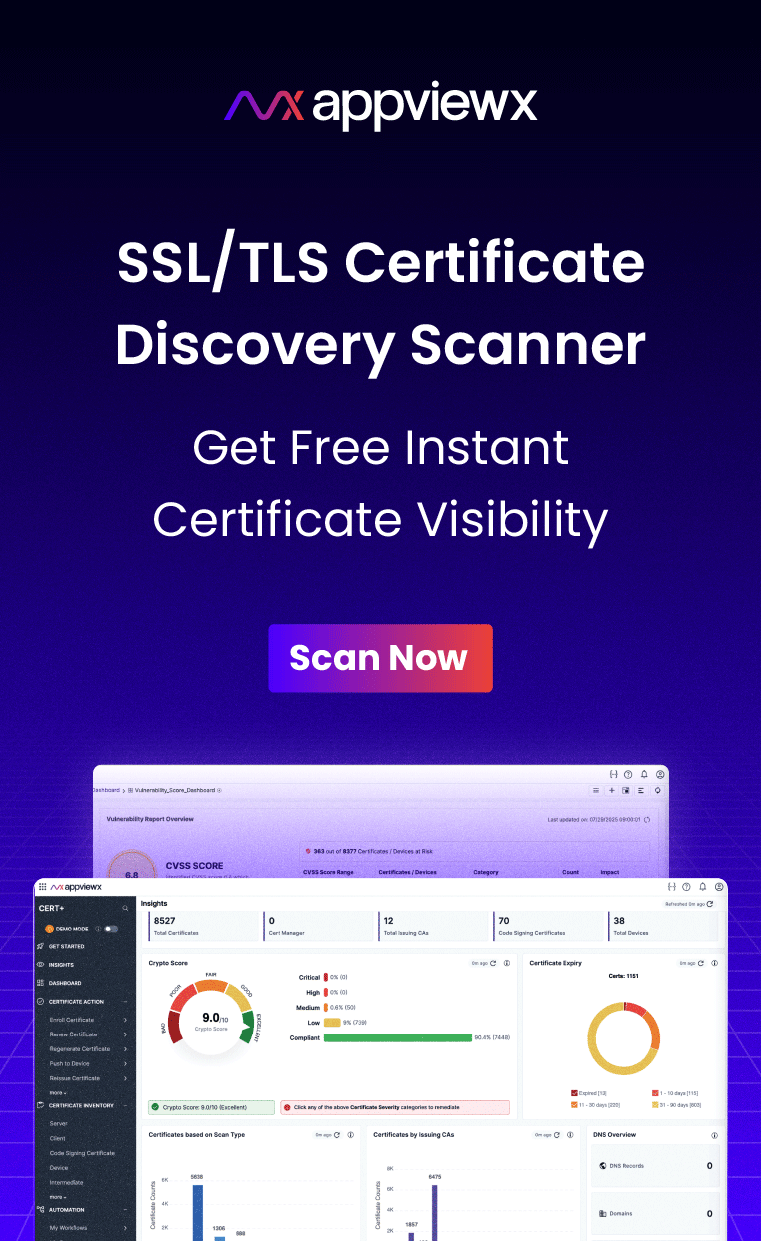
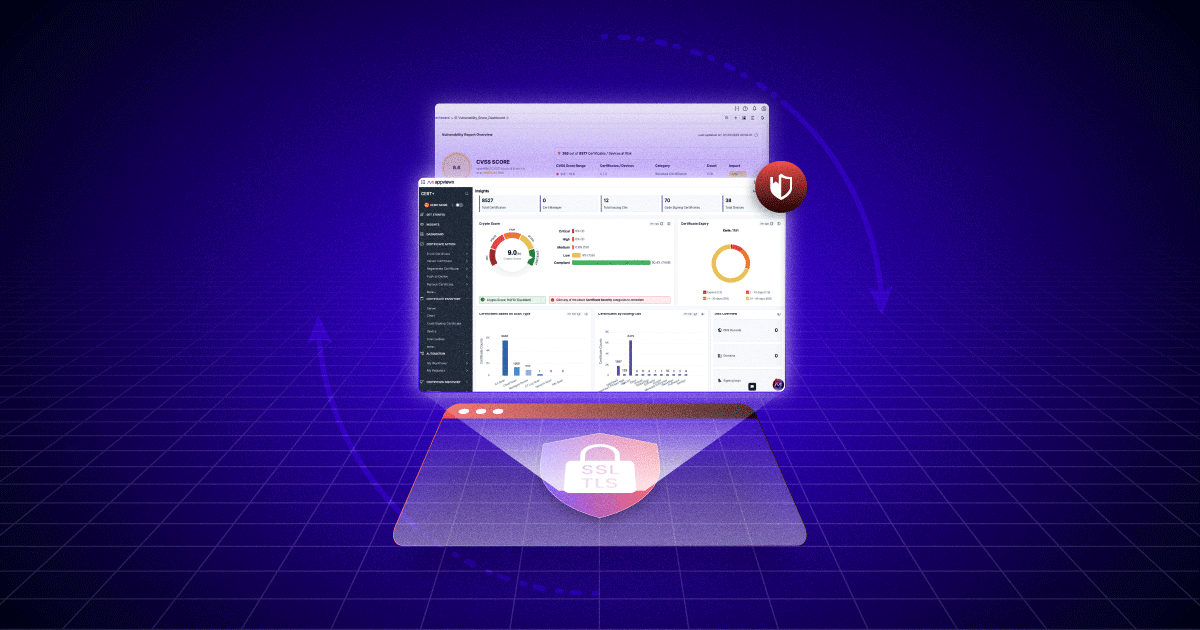
Certificate Lifecycle Management with Visibility, Control and Insights – All in One Place
Key Differences
| Feature | Agent-Based | Agentless |
| Setup Complexity | Requires agent installation on every existing and new endpoint | Centralized and straightforward setup |
| Control Granularity | Device level control | Vendor-agnostic permission controls |
| Compatibility | Suitable for diverse environments with a variety of endpoints | Certified integrations enabling predictability
Can integrate with Privileged Access Management (PAM) for secure session handling and credential management. |
| Scalability | Complex to scale as it requires installing, managing, and maintaining agents on each endpoint | Highly scalable as no agent installation is needed |
| Security | Encrypted storage and local actions | Depends on device-native protocols |
| Maintenance | Ongoing agent updates and configuration changes required | Minimal maintenance |
| Network Dependencies | Operates in disconnected networks | Dependent on the efficiency of the network and protocols |
| Resource Consumption | Agents share resources with the devices on which they are installed | No local resource consumption. All CLM tasks are performed on the main central server. |
| Service Account Management | Needs separate account management for each agent | Simplified service account management through centralized credential rotation or PAM integration. |
Recommendation
1. Agentless is best suited for:
- Quick deployments like cloud-native environments and DevOps pipelines
- Cost-conscious operations involving low maintenance
- Use cases where installing agents isn’t feasible, such as IoT devices, legacy systems, or endpoints bound by strict policies.
- Smaller and more uniform environments or when leveraging native integrations like cloud APIs.
2. Agent-based is best suited for:
- Large-scale, complex environments with diverse device configurations and operating systems, where granular control over certificate management is essential.
- Environments with stringent security and compliance requirements like finance and healthcare that demand robust, endpoint-level protection.
- Environments where agents can enhance automation and manage certificates in isolated or segmented networks.
The choice between agent-based and agentless architectures depends on the specific requirements of your organization’s infrastructure, security posture, and operational goals. Both approaches bring distinct advantages: agent-based provides robust control and security, while agentless delivers simplicity, security, control, cost efficiency, and rapid implementation for streamlined deployments.
With the AppViewX AVX ONE Certificate Lifecycle Management and PKI Platform, you don’t have to settle for one or the other. Supporting both agent-based and agentless architectures, the AVX ONE empowers you to adopt an integrated strategy that maximizes efficiency and scalability across diverse environments.
What sets AppViewX AVX ONE apart is its ability to deliver broader agentless automation. By leveraging API-driven workflows, secure communication protocols, a cloud-native architecture, and extensive pre-built integrations, AVX ONE offers a scalable, secure, and highly flexible solution across a variety of IT environments. This comprehensive approach allows AppViewX to provide more extensive agentless functionality than many of its competitors, who may rely solely on agents. AppViewX also offers agent-based capabilities for deeper system-level access, more complex integrations, or specific environments, delivering adaptability and efficiency in your certificate lifecycle management strategy.
Talk to one of our experts to learn more about the AppViewX AVX ONE CLM and PKI Platform.