Why the 47-Day SSL/TLS Certificate Mandate Matters Now
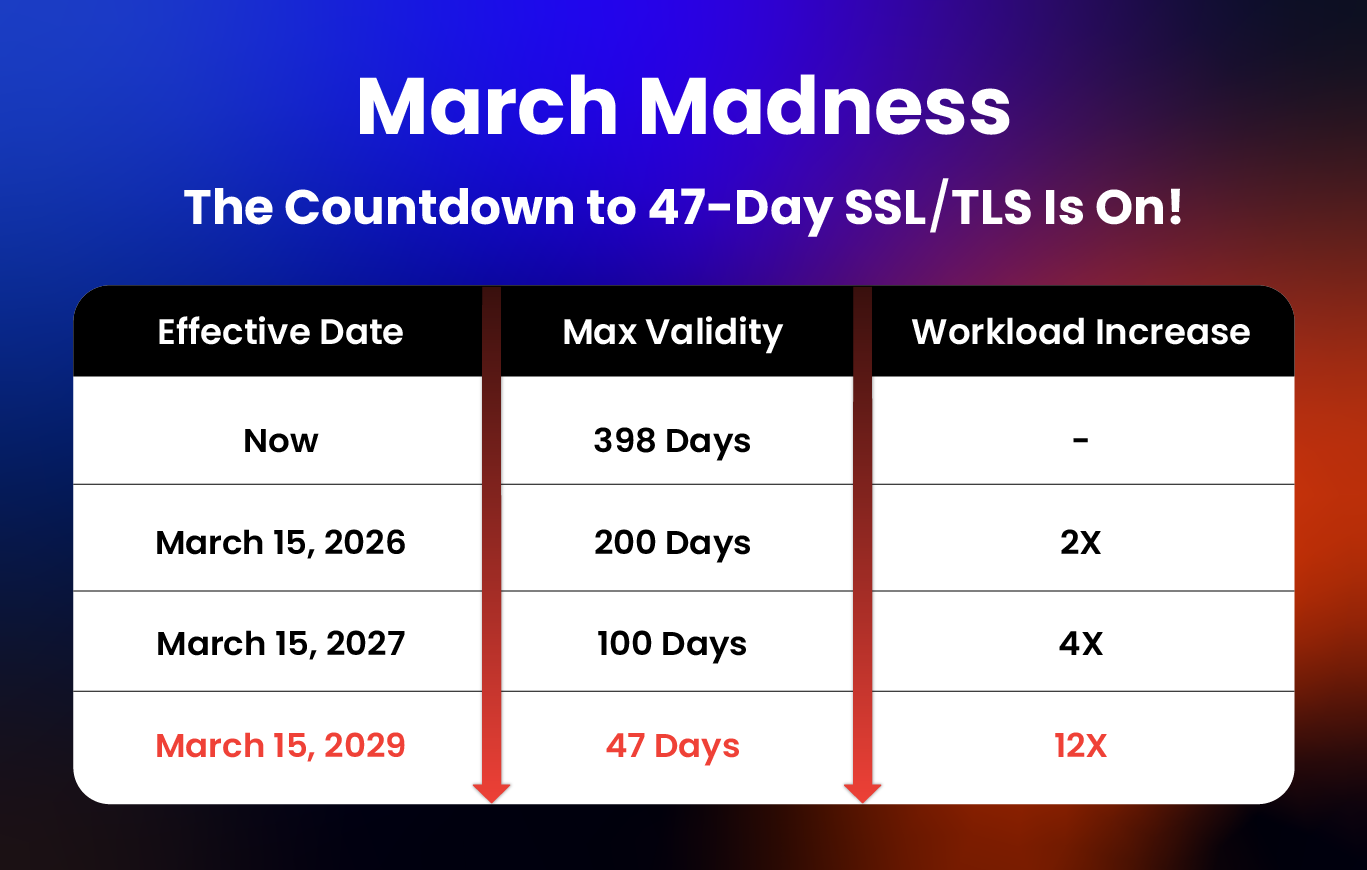
The move to 47-day SSL/TLS certificate lifespans marks a turning point. It reflects the industry’s push for stronger security and crypto-agility. With faster certificate expirations and a 12-fold increase in workloads on the horizon, SSL/TLS certificate management programs will no longer be manageable using manual processes and spreadsheets. Organizations relying on spreadsheets for certificate tracking face increased risk of expired certificates, certificate sprawl, and Shadow IT certificates that create security vulnerabilities. Automation is not only essential but a strategic move towards a crypto-agile future.

The Strategic Upside of Shorter Certificate Lifespans: 7 Reasons to Act Now
Shorter certificate lifespans are an opportunity to modernize, automate, and position your operations for a long-term advantage. It’s a smart business decision and the most resilient organizations are acting now. Here’s why:
- Stronger security posture: Shorter validity windows mean a smaller window for certificates to be exploited. This reduces exposure to man-in-the-middle attacks and certificate-related security breaches.
- Faster adoption of cryptographic standards: Your organization can migrate more quickly to new algorithms and CA requirements, forcing crypto-agility. This positions you for seamless post-quantum cryptography (PQC) migration when quantum computers threaten current encryption methods.
Read More in The Nine Advantages of Preparing for 47-Day Mandates Today
While many organizations are now reacting to the 47-day certificate lifespans passed in April 2025, Google and Apple have been pushing for shorter lifespans for several years.
CLM Automation Templates and Readiness Checklists
Certificate Lifecycle Management automation is essential for 47-day readiness and it starts with clarity and alignment in your program plan. AppViewX and Gartner have published these helpful guides to assessing and setting up your CLM automation for success by setting precise objectives, creating the right foundational PKI architecture, selecting automation platforms wisely, assessing costs vs savings, and aligning teams for long-term success. Read more and download the free reports for a clear breakdown of on-prem vs. SaaS, advice on proof-of-concept testing, and a roadmap for building crypto-agility.
Techniques for Futureproofing Your Program
Planning for what comes next is essential as you prepare for 47‑day certificate lifespans. That’s because many in the CA/B Forum view these mandates as a way to operationalize habits that NIST recommends for post‑quantum cryptography (PQC) readiness. When cryptographically relevant quantum computers emerge, today’s public‑key algorithms will be at risk and organizations will need to reissue and migrate certificates at scale on a compressed timeline. We have seen a version of this before with the shift from SHA‑1 to SHA‑2, where the real drag was manual, ticket‑driven lifecycle work. Shorter expirations are a practical lever to replace spreadsheets with automated discovery, issuance, renewal, installation, and binding so the next large transition becomes planned work rather than an emergency. Private key management and certificate revocation capabilities become critical during cryptographic transitions to maintain security without disruption. Use the techniques below to futureproof your program now:
-
New PKI Realities: How to Prepare for CA/Browser Mandates and PQC Industry expert Chris Bailey recently shared his state of PKI findings with a practical path forward in the face of upcoming changes. Bailey explains what to inventory, where to start, and how to build crypto-agility without disruption so teams can approach the next few years with clarity instead of guesswork.
Watch On Demand
- "How To Prepare for NIST's Post-Quantum Cryptography Standards" Webinar: In this webcast, an expert panel offers vital guidance for transitioning to quantum-resistant encryption. Industry leaders provide strategic insights and practical steps to kickstart your PQC readiness journey.
- "Prepare for PQC – A Foundations Guide to NIST's PQC Standards and Readiness" Report: With quantum advancements threatening to undermine current public-key encryption systems and potentially rendering them obsolete, NIST has finalized its Post-Quantum Cryptography (PQC) standards—marking a pivotal shift in global cybersecurity. As organizations worldwide prepare for this transition, it’s crucial to establish a proactive, multi-year migration strategy to ensure resilience against quantum threats.
Case Studies and Measurable Impacts
Organizations in every sector are adapting to shorter SSL/TLS certificate lifespans and the growing demands of certificate lifecycle management. From healthcare to financial services to large enterprises, the challenges often look the same: too many certificates to track manually, fragmented processes, and increasing renewal workloads. Certificate-related downtime costs $400 billion a year, making certificate outage prevention a critical business priority.
The following case studies highlight how different teams approached these issues, modernized their certificate management practices, and built programs designed to scale with future changes.